- Personal
Personal Banking
PERSONAL LOANS & CREDIT
RETIREMENT & INVESTMENTS
Digital Banking
- Business
Business Banking
BUSINESS LOANS & CREDIT
Business Services
Digital Banking
- Commercial
Commercial Banking
Commercial Loans & Financing
Treasury Management
Additional Commercial Solutions
- Wealth
Private Wealth Management
Institutional Asset Management
Investments
Corporate Underwriting
- About Us
Community Involvement
Company
Our Insights Blog
Our Team


5.00% APY 5-Month CD
Looking for a secure, reliable way to grow your cash savings? Certificates of Deposit (CDs) can help you reach your short-term or long-term savings goals with guaranteed fixed rate returns.

What’s your Goal?
I want to
Freestyle Checking
Get the convenience and flexibility you need from a personal checking account.
- Never worry about NSF fees
- Service charge waived with one qualifying monthly transaction
- Account protection with Visa® Purchase Alerts2

Mortgage solutions
Get flexible terms, competitive rates, and the support of a local home lending expert who can match you with the right mortgage.
- Loans for more established buyers
- Government-backed loans for new borrowers
- Loans for active duty military and veterans

100+ years of turning dreams into businesses
We offer a full suite of business solutions designed to get your business started and help it grow.
- Business loans and lines with flexible terms
- Checking accounts with great service and powerful tools at your fingertips
- Merchant Services solutions to streamline your retail payments

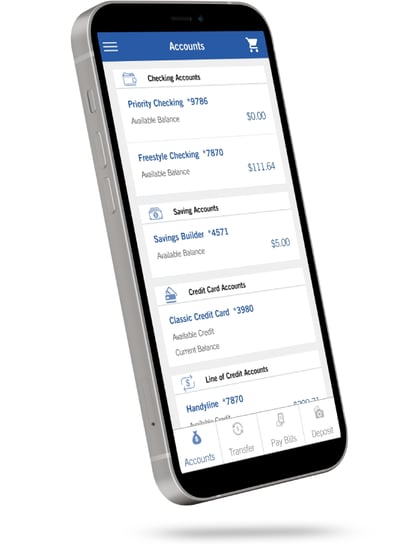
Bank where you want, when you want
Get the convenience of banking on the go or at home, with digital tools that put your account at your fingertips.
Send and receive money with Zelle1
Deposit checks with your smartphone
Shop securely with Mobile Wallet
Pay your bills in one place with Bill Pay
Why your neighbors trust Hancock Whitney
For more than a century, Hancock Whitney has been dedicated to the financial well-being of Gulf South communities.
We give back to our local communities because we're committed to the future of our region.
We're more than a bank—we're a community partner focused on giving back.
Want to explore other ways to reach your financial goals?
1U.S. checking or savings account required to use Zelle®. Transactions between enrolled users typically occur in minutes. Only send money to people you know well and trust. If you don't know the person you are paying or are unsure you will receive what you are purchasing, then we don't recommend you use Zelle® for the transaction. Once you have authorized and made a payment through Zelle®, it may not be possible to reverse the payment or recover the funds.
Zelle® and the Zelle® related marks are wholly owned by Early Warning Services, LLC and are used herein under license.
2Actual time to receive a transaction alert is dependent on wireless service and coverage within area. Message and data rates may apply. Some PIN-based debit transactions may be routed through non-Visa networks. Transactions routed through non-Visa networks will not trigger a purchase alert. For more information about Purchase Alerts, including any limitation and restrictions, go to www.hancockwhitney.com/purchase-alerts.
Apple and the Apple logo are trademarks of Apple Inc., registered in the U.S. and other countries. Apple Pay is a trademark of Apple Inc.
Android is a trademark of Google Inc.
Proud to be an official sponsor of
Hancock Whitney Bank, Member FDIC and ![]() Equal Housing Lender. All loans and accounts subject to credit approval. Terms and conditions apply.
Equal Housing Lender. All loans and accounts subject to credit approval. Terms and conditions apply.
Hancock Whitney and the Hancock Whitney logo are federally-registered trademarks of Hancock Whitney Corporation. © Hancock Whitney 2024
![]()